Sitemap
A list of all the posts and pages found on the site. For you robots out there is an XML version available for digesting as well.
Pages
Posts
Cyber security in healthcare
Published:
Cyber security in healthcare
On January 6, 2025, the U.S. Department of Health and Human Services (HHS) issued a notice of proposed rule making (NPRM), stating significant updates to the HIPAA Security Rule. To strengthen protections for electronically protected health information (ePHI), this revision focuses on improving cyber security practices for better protecting the U.S. health care system, as there has been an increase in cases involving cyber-attacks.
Hackergpt lite
Published:
Hackergpt lite
click the article to read the fill article Hackergpt lite
With a dynamic and intelligent architecture mirroring the decision-making processes of a human penetration tester, application accelerates skill acquisition, by bridging the knowledge gap between novice and expert penetration testers. As the NSA’s cyber-security director, Dave Lube states in one of his interviews that “AI brings unprecedented opportunity, but also can present an ocean of opportunities for malicious activity”, HackerGPT Lite aims to equip users to stay ahead, by empowering users to perform a wide range of security assessments. With its conversational interface, the AI companion delivers real-time insights using powerful tools. This allows users to efficiently perform security assessments and manage complex OSINT tasks with ease, all in a streamlined and intuitive manner. It's like a swiss army knife for cyber security enthusiasts, something that gives you access to a variety of tools in one place, but without the headache of learning how to use each one individually.
Discover and understand your security needs with HackerGPT Lite:
To get started, users must register an account on hackergpt.app to utilize the features and functionalities of HackerGPT Lite. Users can use secure Google Social Login, to register an account and utilize the full power of Gen AI OSINT and Discovery testing tools.
Finra penetration testing 2
Published:
Finra penetration testing 2
Penetration Testing for FINRA Financial Industry Regulatory Authority (FINRA), a not-for-profit organization that regulates broker-dealers and their personnel in the United States, plays a pivotal role in providing guidance on best practices for financial firms to protect their systems and data. In 2024, FINRA published a report that examines and provides recommendations to member firms with rich insight into findings from its Member Supervision, Market Regulation and Enforcement program. These guidelines and recommendations provide greater transparency to member firms and the public about regulatory and compliance activities. While FINRA itself does not prescribe a specific penetration testing (pentesting) requirement, firms must adhere to general cyber security standards as part of their compliance obligations under FINRA Rule 4370 (Business Continuity Plans) and FINRA Rule 3110 (Supervision). With financial firms facing persistent threats of phishing, insider threat activities, and common vulnerabilities due to branch office controls, it is important for firms to maintain a strong cyber security framework capable of deploying vigilant and robust defensive and proactive measures.
White hat vs black hat
Published:
White hat vs black hat
click the article to read the fill article White hat vs black hat
"There are only two types of companies: those that have been hacked and those that will be hacked” states Robert Mueller, former Director of the FBI emphasizing on the evolving intricate domain of cyber-security . As modern technology relentlessly pushes the boundaries of innovation breaking new frontiers, every organization increasingly becomes a potential target for malicious hackers. This rapid advancement not only opens up new opportunities but also exposes vulnerabilities that cyber-criminals are eager to exploit. Maintaining robust security measures has evolved from being merely important to absolutely essential for operational integrity.
A Guide for Data Science Projects in 2023
Published:
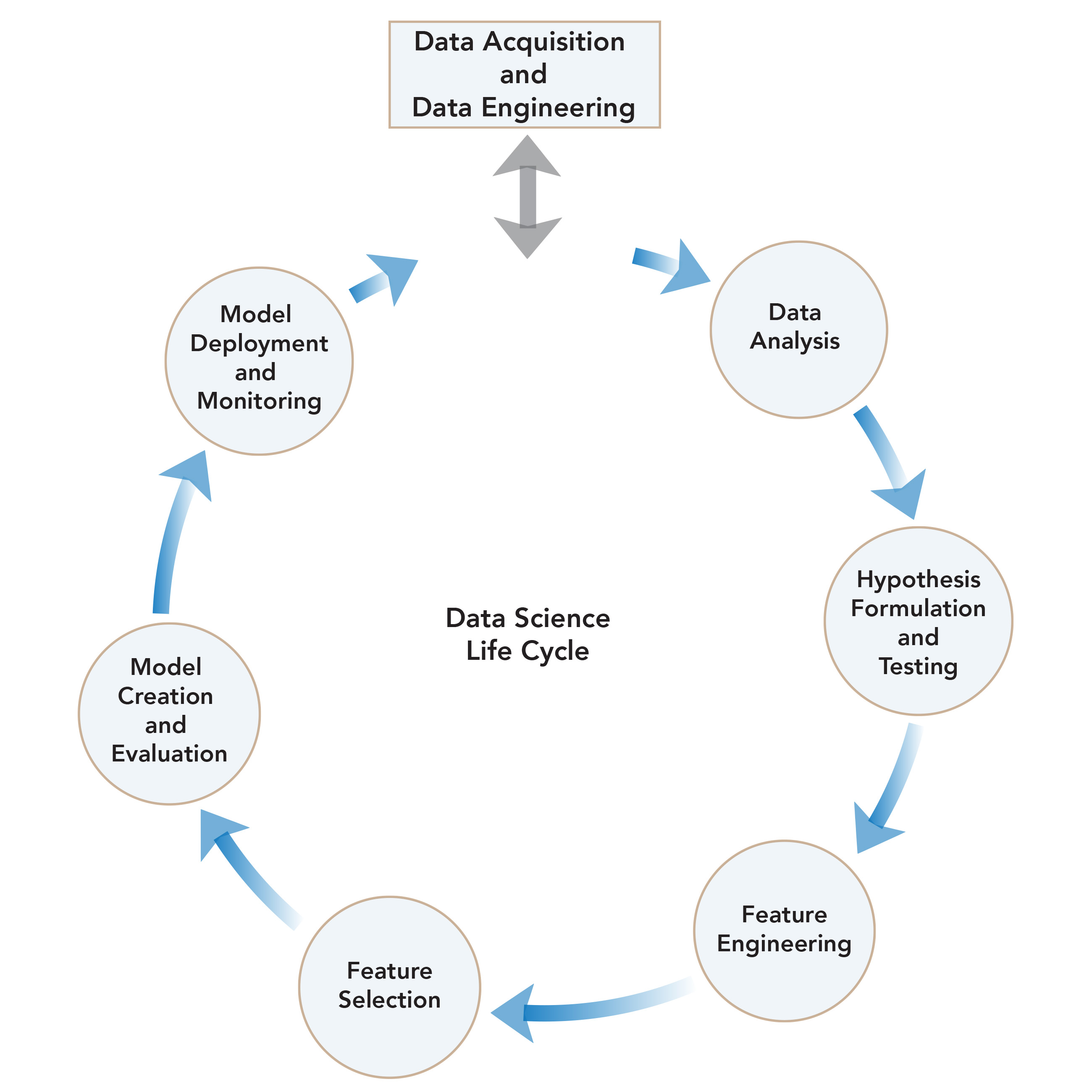
This post explains how to define a problem statement and perform the necessary tasks to achieve meaningful results. It provides a walkthrough of a structured approach to ensure the successful completion of a data science project.  —
—
project
Data-Challenge-2022-UB
Accurate intervention of suicidal ideation and behavior in depressed people can help them get the therapeutic help and care they need, which can save their lives in many scenarios. The goal is to precisely anticipate data in order to avert incidents such as suicide and to assist people in overcoming depression
E-wal
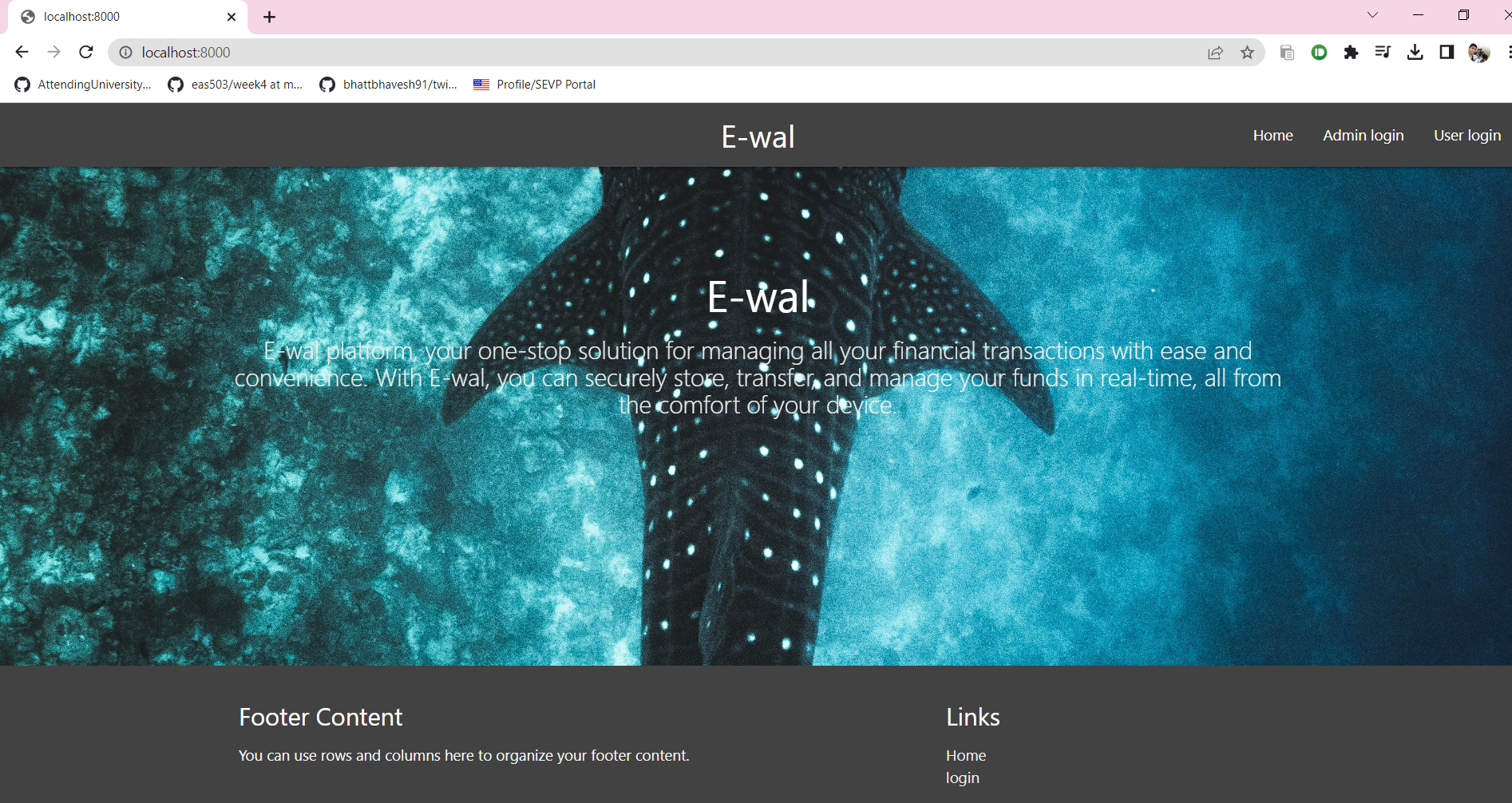
Payment Web Application
pneumonia_detector(Chest x_ray CNN)
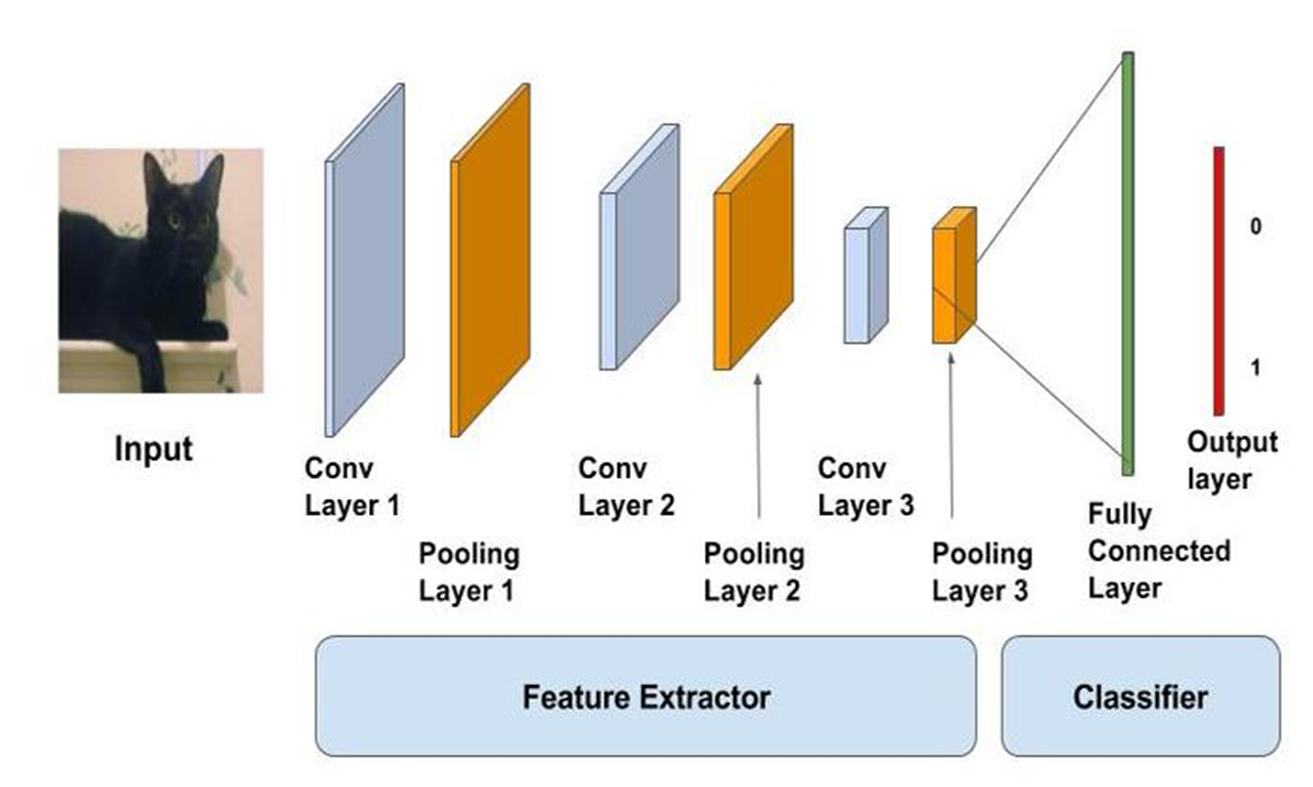
This application uses artificial neural network as a filter to classify the image. The output of the neural network is scaled so as to get the proper sizes of the images that are classified and can be used by radiologists to predict the abnormality up to a great extent.
US Rent Price Prediction
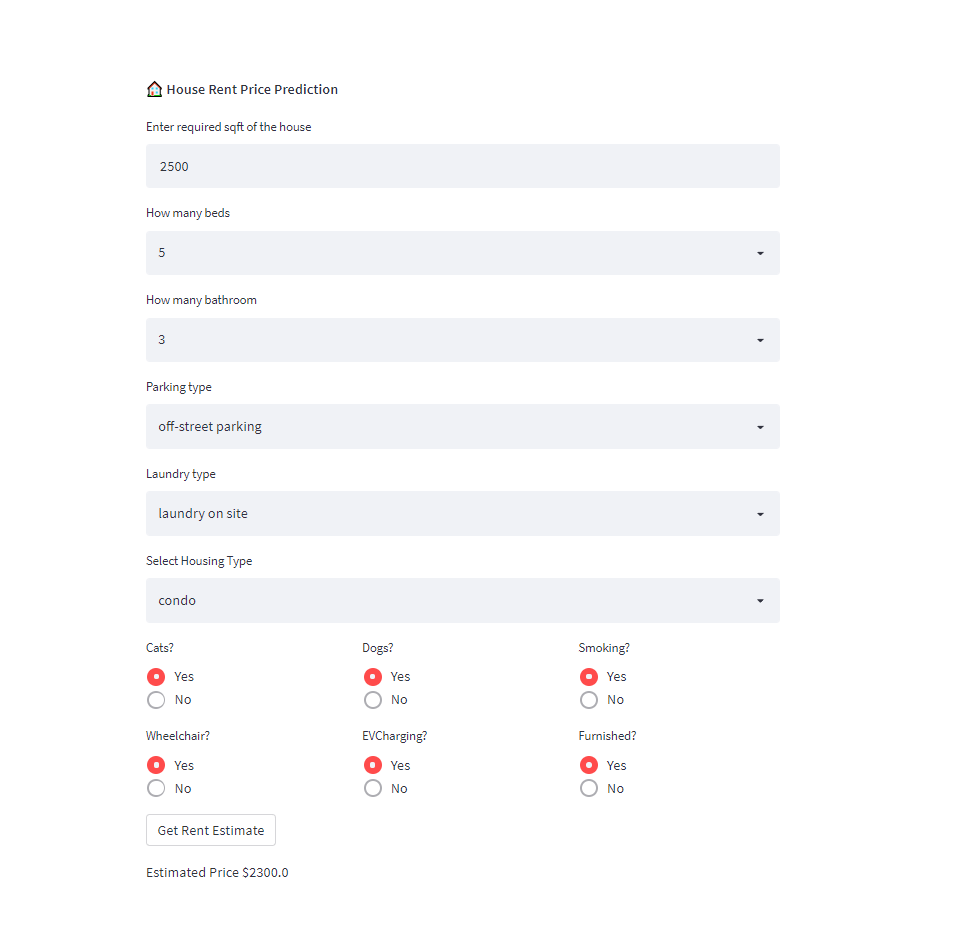
The goal of the project is to analyze the rental postings across the United States and provide actionable insights to the users in form of graphs and intuitive user interface.
publications
Gesture Based Spatio-Temporal Representation Learning for Robust Fingerprint Presentation Attack Detection
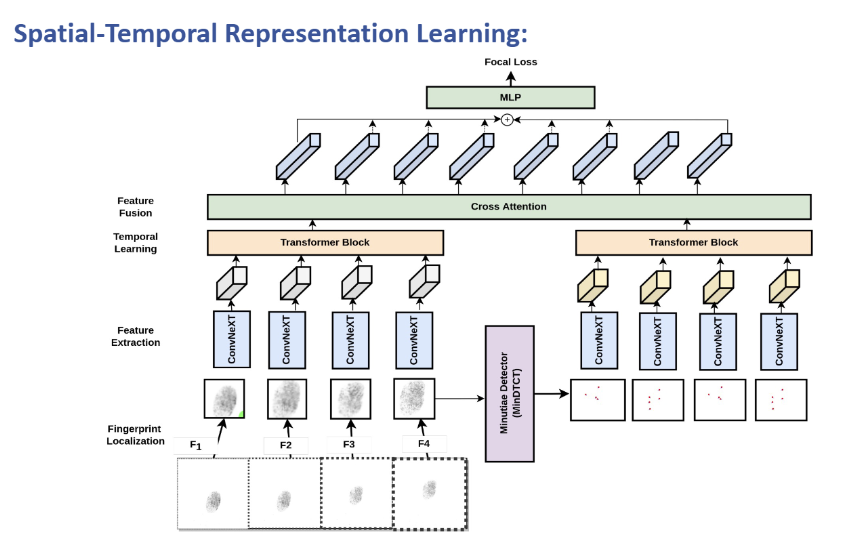
Published in 2024 IEEE 18th International Conference on Automatic Face and Gesture Recognition (FG) , 2024
- Fingerprint spoof attacks are highly common and pose a significant threat to biometric security systems.
- Existing methods primarily focus on image classification, ignoring the potential benefits of temporal learning.
- The differences in the elastic properties of real versus fake fingerprints can be better detected through motion-induced gestures.
- Widely used datasets lack temporal information, prompting the creation of a new dataset to explore distortion-based spoof detection.
Recommended citation: @inproceedings{sankaran2019representation, title={GestSpoof: Gesture Based Spatio-Temporal Representation Learning For Robust Fingerprint Presentation Attack Detection}, author={Bhavin Jawade, Shreeram Subramanya, Atharv Dabhade, Srirangaraj Setlur, Venu Govindaraju}, booktitle={2024, 18th IEEE International Conference on Automatic Face & Gesture Recognition (FG 2024)}, year={2024}, organization={IEEE} }
Download Paper
research
GestSpoof - FG 2024
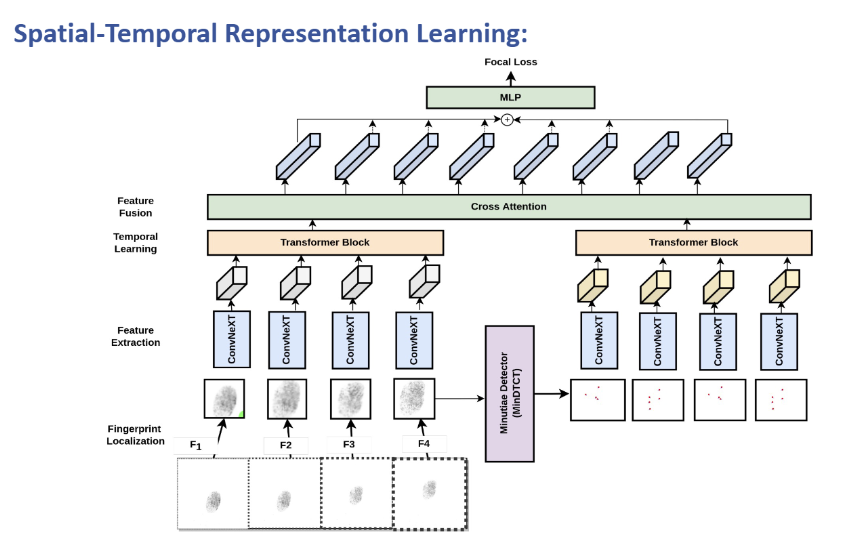
GestSpoof: Gesture Based Spatio-Temporal Representation Learning For Robust Fingerprint Presentation Attack Detection. - FG 2024
HackerGPT Lite

HackerGPT Lite: An AI OSINT and Discovery Tool
